Ciphers and Cybersecurity in Other Fields
Cybersecurity First Principles in this lesson
-
Data Hiding: Data hiding is the technique that does not allow certain aspects of an object to be observed or accessed. Data and information hiding keeps the programmer from having complete access to data structures. It allows access to only what is necessary.
-
Layering: Cyber security uses multiple layers of defense or protecting information. If one layer is defeated the next layer should catch it.
-
Least Privilege: One of the ways to protect information is by limiting what people can see and do with your information and resources. The principle of least privilege says to allow the minimum number of privileges necessary to accomplish the task.
-
Pre-digital era Ciphers: Transposition ciphers – rearrange the order of the characters of plaintext also called permutation ciphers The arrangement becomes the key Substitution ciphers – replace the characters with something else (e.g. another character or number) The replacement function becomes the key
Introduction
In this lesson, we will learn about ciphers and basic cryptography and how it can apply to cybersecurity and other areas of education. We will go over a brief history of the usage of ciphers and how they work.
Goals
By the end of this tutorial, you will be able to:
- Understand and be able to describe
data hiding,layering, andleast privilegein terms of cryptography - Encrypt and decrypt simple messages using different Ciphers
Materials Required
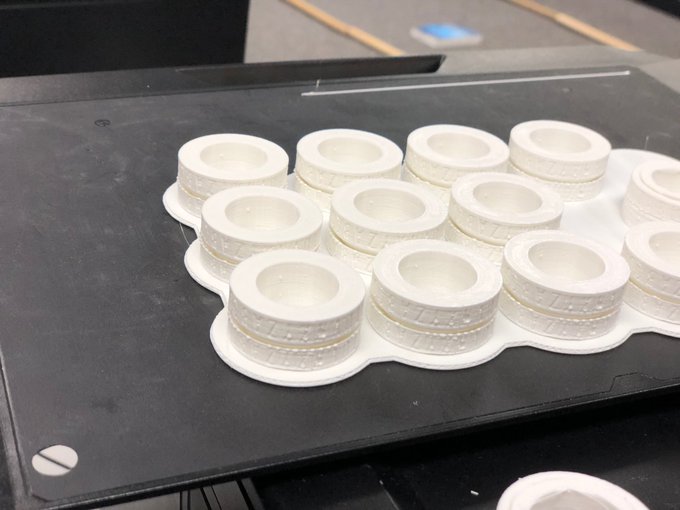
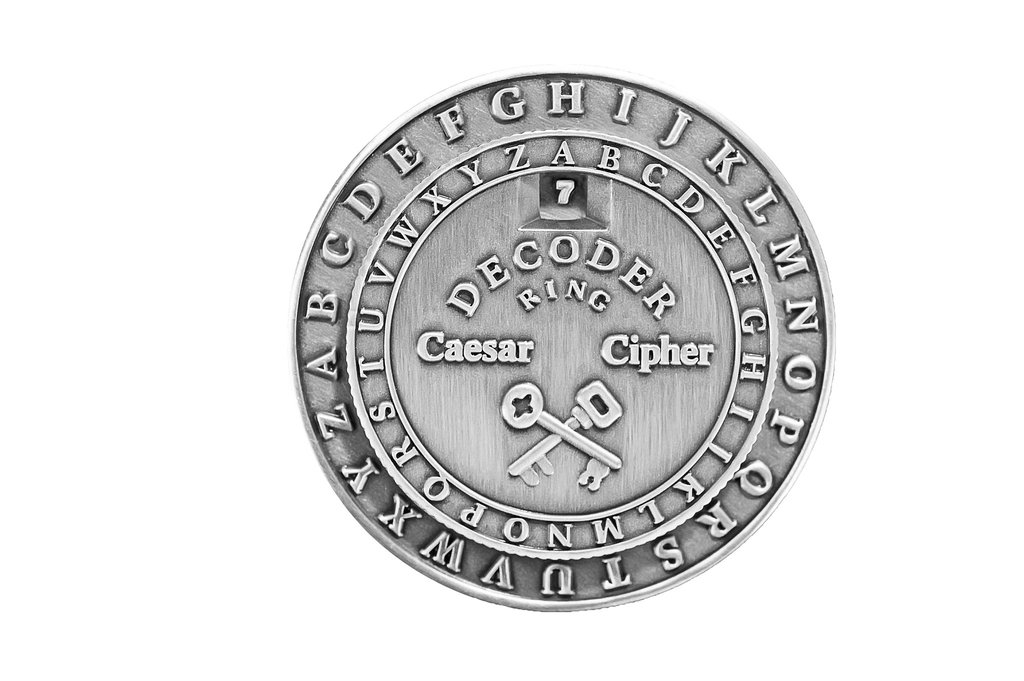
- Cipher Wheels
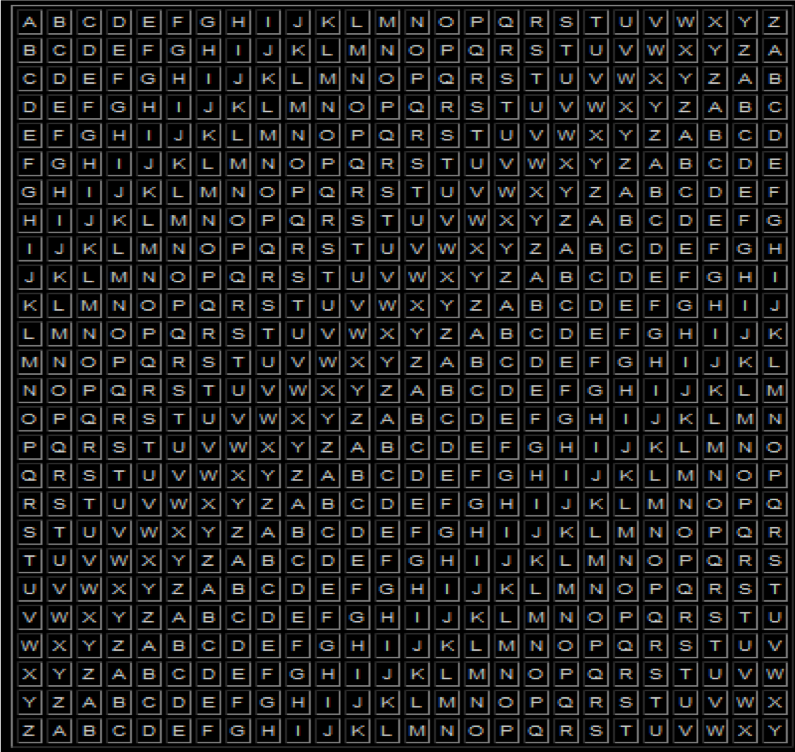
- Vigenere Square
Prerequisite lessons
None
Table of Contents
- Basic Terms
- Cybersecurity First Principles in this lesson
- Introduction
- Goals
- Materials Required
- Prerequisite lessons
- Table of Contents
- Step 1: Learn all the words!
- Step 2: Ciphers
- Step 3: Cryptoanalysis
- Step 4: Practice Decrypting and Encrypting
- Self Exploration
- Test Your Bits, err… Wits!
- Additional Resources
- Acknowledgements
- License
Step 1: Learn all the words!
Plaintext/Cleartext - an unaltered message as it’s intended to be read
Ciphertext – message that has been changed so its meaning is concealed
Encryption/enciphering – changing plaintext to ciphertext
Decryption/deciphering – changing ciphertext back into plaintext
Key – secret value needed to encrypt and/or decrypt
Cryptographic Algorithm/cipher – a standard sequence of computational steps to encrypt or decrypt a message using a key
Cryptanalysis – practice of analyzing encrypted messages to reveal the plaintext without knowing the key
Strength – determines how much effort and how long it takes to break a ciphertext
Step 2: Ciphers
- Zig-Zag and Route Crypto
- Civil War Crypto Sticks
- Caesar Ciphers
- Vigenere Square
- Enigma Machine
We will discuss the usages and history of each of these ciphers.
Step 3: Cryptanalysis
- Frequency
By doing frequency analysis to see which letters appeared most often then substituting most frequent plain text letter, could break the cipher. - Language characteristics
If spaces are left in, then characteristics like single letter and 2 letter words are still in tact and knowledge of these can be utilized to help in breaking Having a longer message only makes both things easier to spot
Step 4: Practice decrypting and encrypting
Using the cipher rings we will practice encoding and decoding.
Self Exploration
Try some different encryption yourself.
Reflection
In this lesson, we saw how encryption can be used for data hiding. Multiple encryption rounds can also be used as for layering.
Additional Resources
For more information, investigate the following:
- NSA Cytptochallenges - Puzzle of the week
- NSA CryptoKids
Lead Author
- Chris Daniels
Acknowledgements
Special thanks to Dr. Robin Gandhi for reviewing and editing earlier versions of this lesson.
License
Nebraska GenCyber 
is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License.
Overall content: Copyright (C) 2017-2018 Dr. Matthew L. Hale, Dr. Robin Gandhi, Dr. Briana B. Morrison, and Doug Rausch.
Lesson content: Copyright (C) Chris Daniels 2017.

This lesson is licensed by the author under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License.